AI Summary
- This blog post dives into the transformative power of zero-knowledge proofs in blockchain technology.
- While blockchains offer transparency, they fall short in protecting sensitive data.
- Zero-knowledge proofs revolutionize verification by confirming statements without revealing underlying inputs.
- The post explores how this innovation revolutionizes Layer 2 scaling, blockchain interoperability, data storage, smart contract privacy, identity verification, supply chain collaboration, and financial integrity verification.
- Real-world implementations like zkSync, zkBridge, and Tornado Cash showcase the practical applications of zero-knowledge proofs.
Blockchains were built on transparency. Every transaction, balance, and state change is visible and verifiable by anyone. This design removes reliance on central authorities, but it introduces a major limitation. Sensitive data cannot remain private.
Zero-knowledge proofs address this limitation by changing how verification works. Instead of revealing data to prove correctness, a system can generate a proof that confirms a statement is valid without exposing the underlying inputs. This allows blockchains to verify transactions, computations, and identities while keeping critical information hidden.
This blog examines how zero-knowledge proofs are applied across key blockchain use cases, including Layer 1 architectures, Layer 2 scaling systems, interoperability frameworks, and more.
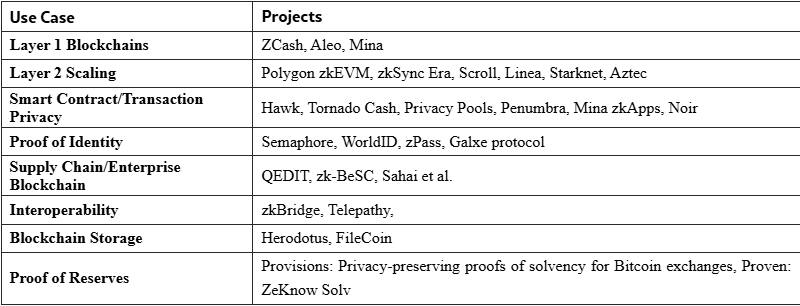
Core Blockchain Applications of ZK-Proofs
1. Layer 2 Scaling: ZK Rollups as a Modular Execution Layer
Business Problem
Layer 1 blockchains face structural limits:
- High transaction costs due to limited block space
- Low throughput under network congestion
- Requirement for every node to re-execute transactions
These constraints make it difficult to support high-volume applications such as payments, trading platforms, and enterprise-grade systems.
ZK-Based Approach
Zero-knowledge rollups address this by separating execution from verification.
- Transactions are executed off-chain
- State transitions are summarized into a proof
- Layer 1 validates the proof instead of re-running the computation
This model allows organizations to process large transaction volumes while relying on Layer 1 for final settlement
Real-World Implementations
- zkSync Era
EVM-compatible rollup with native account abstraction and custom compiler optimizations - Polygon zkEVM
Focuses on EVM equivalence, allowing direct deployment of existing smart contracts - Scroll
Maintains compatibility with minimal opcode adjustments - Linea
Supports standard Ethereum tooling with strong developer continuity - StarkNet
Uses STARK proofs and a custom language (Cairo), prioritizing scalability and transparency
2. Blockchain Interoperability: Cross-Chain Verification Without Trust Dependencies
Business Problem
The blockchain ecosystem is highly fragmented. Organizations operate across:
- Multiple Layer 1 networks
- Layer 2 rollups with isolated state
- Application-specific chains
This fragmentation creates operational challenges:
- Asset transfers require intermediaries
- Data cannot move freely across networks
- Cross-chain coordination introduces security risks
Traditional bridge models rely on trusted relayers or multisig systems, which increase exposure to failures and exploits.
ZK-Based Approach
Zero-knowledge proofs enable direct verification of state across chains.
Instead of trusting intermediaries, a receiving chain can verify:
- That a transaction occurred
- That a state transition is valid
- That a block has reached finality
This is done through cryptographic proofs rather than third-party validation.
Real-World Implementations
zkBridge
- Uses a block header relay network
- Generates zkSNARK proofs for correctness
- Maintains verified headers on the destination chain
- Provides a general interface for cross-chain applications
Telepathy
- Enables message passing across chains
- Uses zkSNARKs to prove Ethereum block finality
- Combines:
- Proof of validator signatures
- Merkle proofs for transaction inclusion
- Executes verified messages on the destination chain
Need Help Choosing the Right ZK Stack
3. Blockchain Storage: Verifying Data Without Storing It On-Chain
Business Problem
Storing large volumes of data directly on-chain is expensive and difficult to scale.
Challenges include:
- High storage costs
- Increased verification overhead
- Growth in proof size as datasets expand
Traditional approaches rely on Merkle proofs to verify data inclusion. As datasets grow, these proofs become larger and more costly to validate, making them unsuitable for high-volume or enterprise-grade applications.
ZK-Based Approach
Zero-knowledge proofs introduce a different model.
Instead of storing and verifying full datasets on-chain:
- Data is stored off-chain
- Computation is performed off-chain
- A compact proof is generated to confirm correctness
The blockchain only verifies the proof, not the underlying data or computation.
Real-World Implementations
Herodotus
- Introduces storage proofs for blockchain data
- Enables access to historical Ethereum data
- Combines:
- Inclusion proofs
- Computation proofs
- Uses STARK-based systems for verification
Filecoin
- Uses distributed storage across global nodes
- Applies zkSNARKs to generate compact proofs
- Enables fast and low-cost verification
- Reduces verification overhead significantly compared to traditional methods
4. Smart Contract and Transaction Privacy: Selective Confidentiality on Public Blockchains
Business Problem
Public blockchains expose all transaction details and smart contract interactions.
This creates limitations for use cases that require confidentiality, such as:
- Financial transactions
- Auction mechanisms
- Treasury management
- Sensitive business logic
Organizations need a way to operate on public infrastructure while controlling data visibility.
ZK-Based Approach
Zero-knowledge proofs enable selective privacy at the application layer.
- Computation involving sensitive data is performed off-chain
- A proof is generated confirming correctness
- The proof is verified on-chain without revealing inputs
This allows applications to maintain confidentiality while preserving verifiability.
Real-World Implementations
Tornado Cash
- Enables transaction mixing on Ethereum
- Uses zkSNARKs to prove membership in a deposit set
- Prevents double-spending using nullifiers
Operational constraints:
- Anonymity set depends on user participation
- Fixed transaction denominations
- Timing analysis can reduce privacy
5. Proof of Identity: Verifiable Credentials Without Data Exposure
Business Problem
Digital identity systems require users to share sensitive information to access services.
This creates several risks:
- Exposure of personal data
- Centralized storage vulnerabilities
- Repeated KYC processes across platforms
- Lack of user control over identity data
Organizations need a model where identity can be verified without transferring or storing raw personal information.
ZK-Based Approach
Zero-knowledge proofs enable identity verification based on cryptographic commitments rather than direct disclosure.
A user can prove:
- Membership in a group
- Ownership of credentials
- Eligibility for access
Without revealing:
- Personal identity
- Underlying data
- Credential details
Verification is performed on-chain through smart contracts.
Real-World Implementations
Semaphore
- Enables anonymous signaling on Ethereum
- Users prove membership in a group without revealing identity
- Uses:
- Merkle tree inclusion proofs
- Nullifiers to prevent double-use
- Signature verification within proof circuits
World ID
- Proof-of-personhood system
- Built on top of Semaphore
- Verifies that a user is unique without exposing identity details
Galxe Protocol
- Aggregates multiple identity credentials into a single structure
- Enables users to prove specific attributes across platforms
- Uses zkSNARKs with Poseidon-based commitments
zPass (Aleo)
- Enables identity verification using real-world documents
- Supports selective disclosure of attributes
- Designed for integration with privacy-first blockchain environments
6. Supply Chain and Enterprise Blockchain: Secure Data Collaboration Without Exposure
Business Problem
Enterprise and supply chain environments involve multiple stakeholders sharing sensitive data, including:
- Pricing and contracts
- Inventory levels
- Production schedules
- Supplier relationships
Public blockchains introduce transparency, which conflicts with the need to protect business-critical information.
Organizations require a model that supports:
- Data verification
- Cross-party coordination
- Controlled data access
Without exposing proprietary information.
ZK-Based Approach
Zero-knowledge proofs enable organizations to validate business processes and data conditions without sharing the underlying data.
This allows participants to:
- Prove compliance
- Verify product authenticity
- Confirm transaction validity
While keeping internal records private.
Real-World Implementations
QEDIT
- Provides privacy-enhanced enterprise data collaboration
- Enables secure analytics and reporting
- Integrates with existing databases
zk-BeSC
- Supply chain framework using polynomial-based proofs
- Supports confidential transactions between participants
- Demonstrates reduced verification cost on Ethereum
Hyperledger-Based Models
- Combine permissioned blockchain with ZK proofs
- Support:
- Product tracking
- Data privacy
- Process verification
7. Proof of Reserves: Verifiable Financial Integrity Without Disclosure
Business Problem
Financial platforms, especially digital asset exchanges and custodians, are required to demonstrate that they hold sufficient reserves to cover user liabilities.
Traditional approaches rely on:
- Third-party audits
- Periodic reporting
- Trust in centralized entities
These models introduce risks:
- Limited transparency between audits
- Potential misreporting
- Exposure of sensitive financial data
Organizations need a method to prove solvency continuously without revealing internal financial details.
ZK-Based Approach
Zero-knowledge proof of reserves enables institutions to demonstrate that their assets meet or exceed liabilities without disclosing:
- Individual account balances
- Total reserve amounts
- User identities
This is achieved through cryptographic commitments and proof systems that validate financial integrity while preserving confidentiality.
Real-World Implementations
Provisions
- Designed for cryptocurrency exchanges
- Enables proof of solvency without exposing balances
- Demonstrates that liabilities are fully backed by assets
Proven (ZeKnow Solv)
- Provides a platform for financial verification
- Enables institutions to prove liquidity positions
- Focuses on maintaining confidentiality while validating financial health
Ready to Apply Zero-Knowledge Proofs to Your Use Case
Conclusion
Zero-knowledge proofs are not a single solution applied uniformly. They form a flexible framework that adapts to different layers and business requirements. For organizations evaluating blockchain architecture, the focus should not be on adopting zero-knowledge proofs as a feature, but on identifying where proof-based verification replaces existing trust assumptions. This is where the strongest value emerges.